We present a comprehensive overview of Which Cyber Protection Condition Cpcon Establishes. This comprehensive guide covers the essential aspects and latest developments within the field.

Which Cyber Protection Condition Cpcon Establishes remains a foundational element in understanding the broader context. Our automated engine has curated the most relevant insights to provide you with a high-level overview.
"Which Cyber Protection Condition Cpcon Establishes represents a significant milestone in our collective understanding of this niche."
Below you will find a curated collection of visual insights and related media gathered for Which Cyber Protection Condition Cpcon Establishes.
Curated Insights
Captured Moments

Which Cyber Protection Condition Establishes a Protection Priority - Go

Which Cyber Protection Condition Establishes a Protection Priority - Go

Which Cyber Protection Condition Establishes a Protection Priority - Go
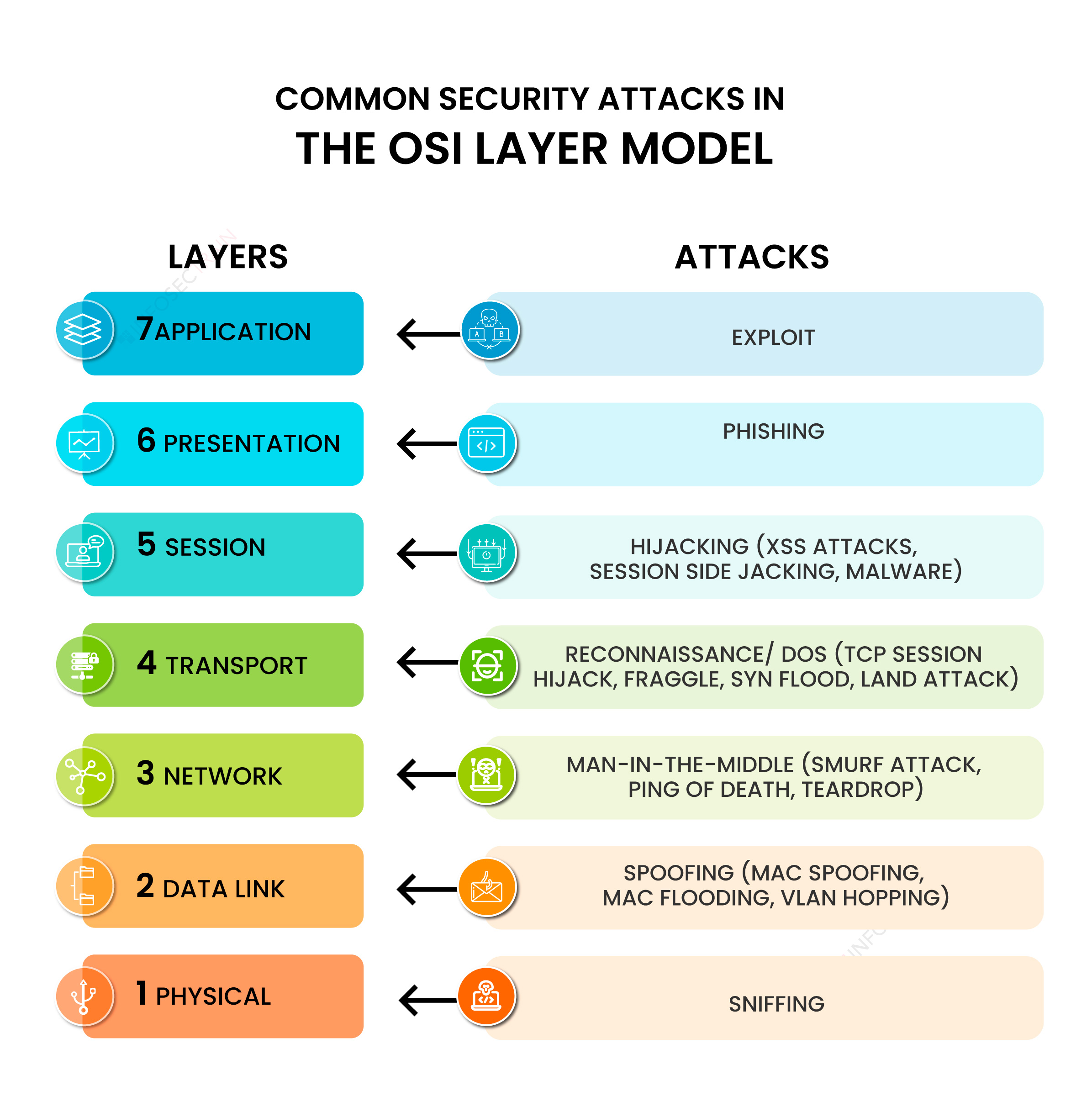
Common Security Attacks in the OSI Layer Model
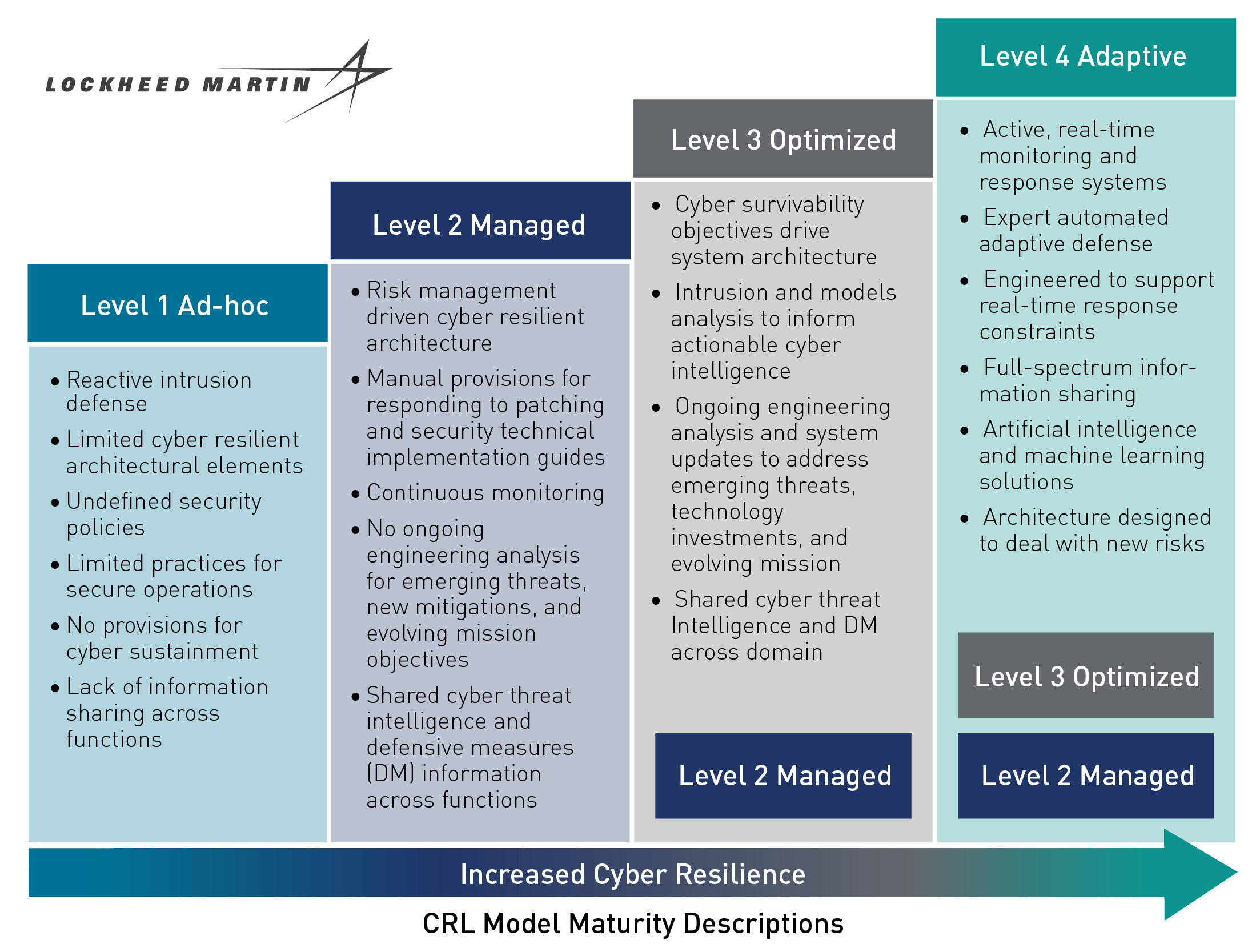
New Model Standardizes Measurement of Cybersecurity in Critical DoD

Cybersecurity Checklist for Remote Working

Top 10 Trends in Cybersecurity, 2022: Combating Industrialized

Coast Guard 2003 Cyber Protection Team establishes new command > United

8 Essential Policies & Procedures for Improved Cyber Security | KBI

National Cybersecurity & Communications Integration Center | Homeland

Coast Guard 2003 Cyber Protection Team establishes new command > United

Internet safety tips – Artofit
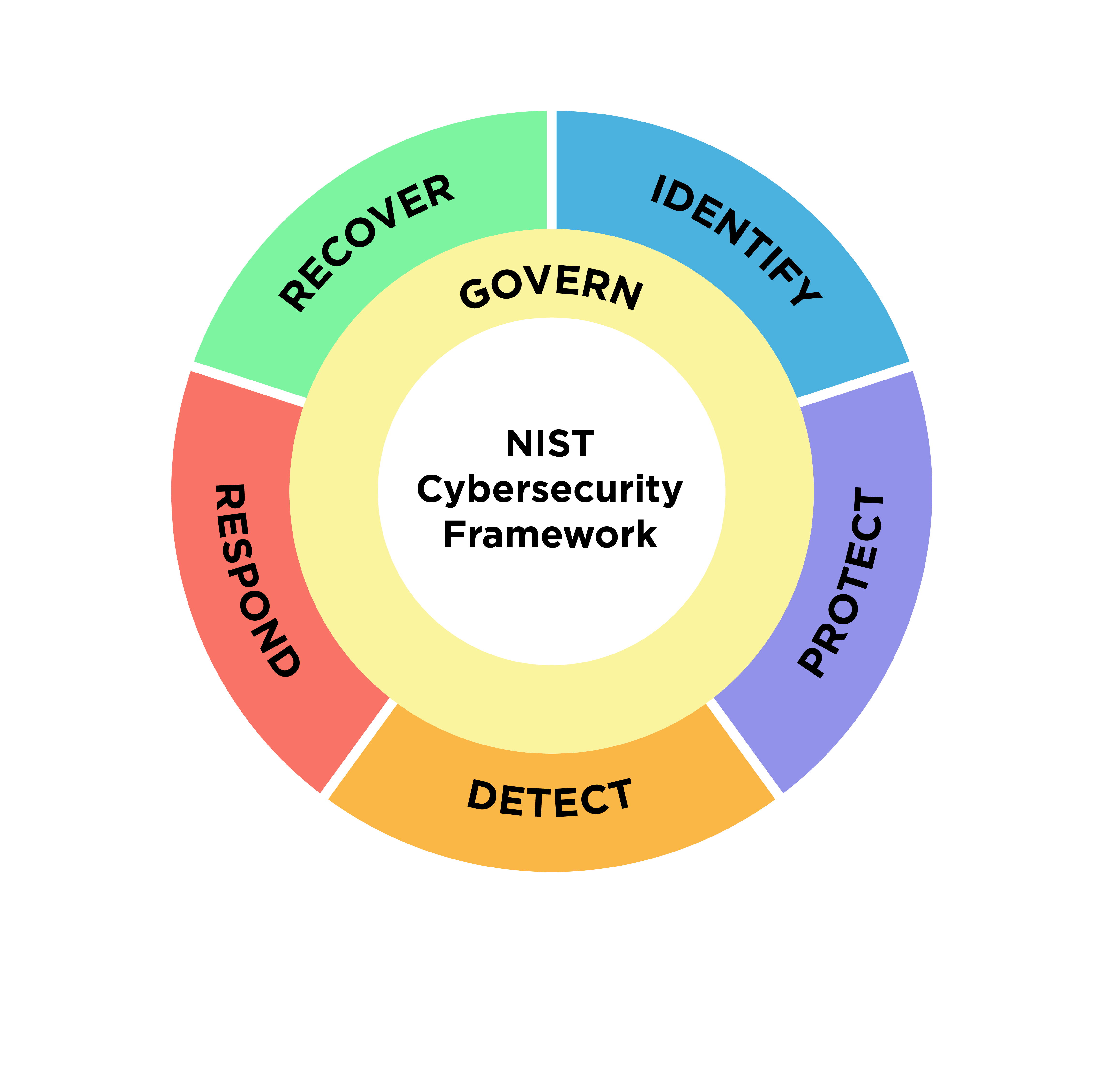
What Is A Cybersecurity Framework | Robots.net

Infographic: Ten steps to cyber security - SAFETY4SEA

What is cybersecurity? A guide to the methods used to protect computer
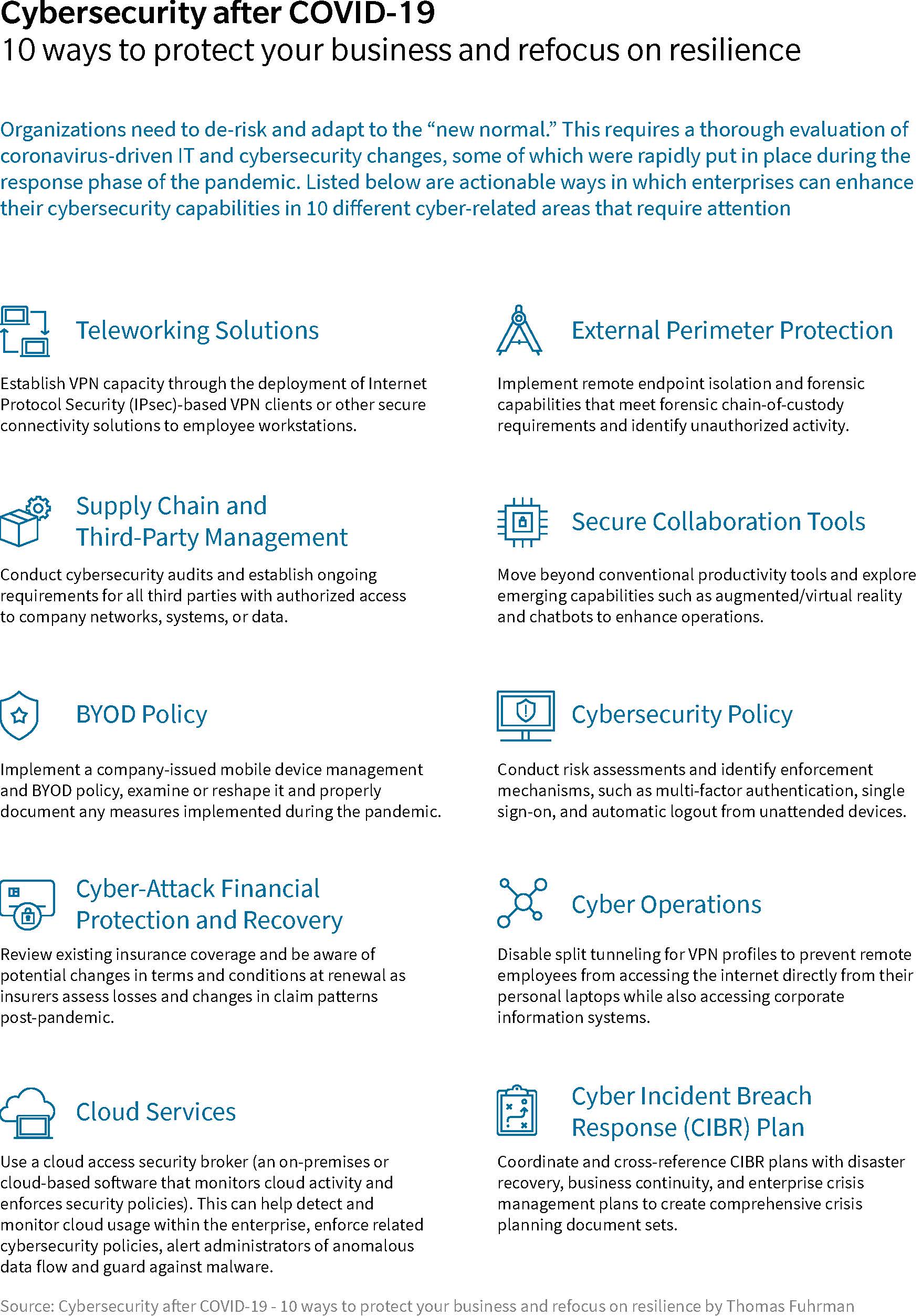
Cybersecurity After COVID-19: 10 Ways to Protect Your Business and

Coast Guard 2003 Cyber Protection Team establishes new command > United

The White House now has a color-coded scale for cybersecurity threats

Protect Against Cyber-attacks with Rate Limiting | US Signal

Free Vector | Protection against cyber attacks infographic

Get Equipped With Advanced Cyber Security Services | RAXA

Threat modeling explained: A process for anticipating cyber attacks
Cybersecurity terms that you need to understand | Peak I.T.

7 Cybersecurity Basics For Your Business - Global IT Services

Multimedia Gallery - Infographic showing how NSF-supported
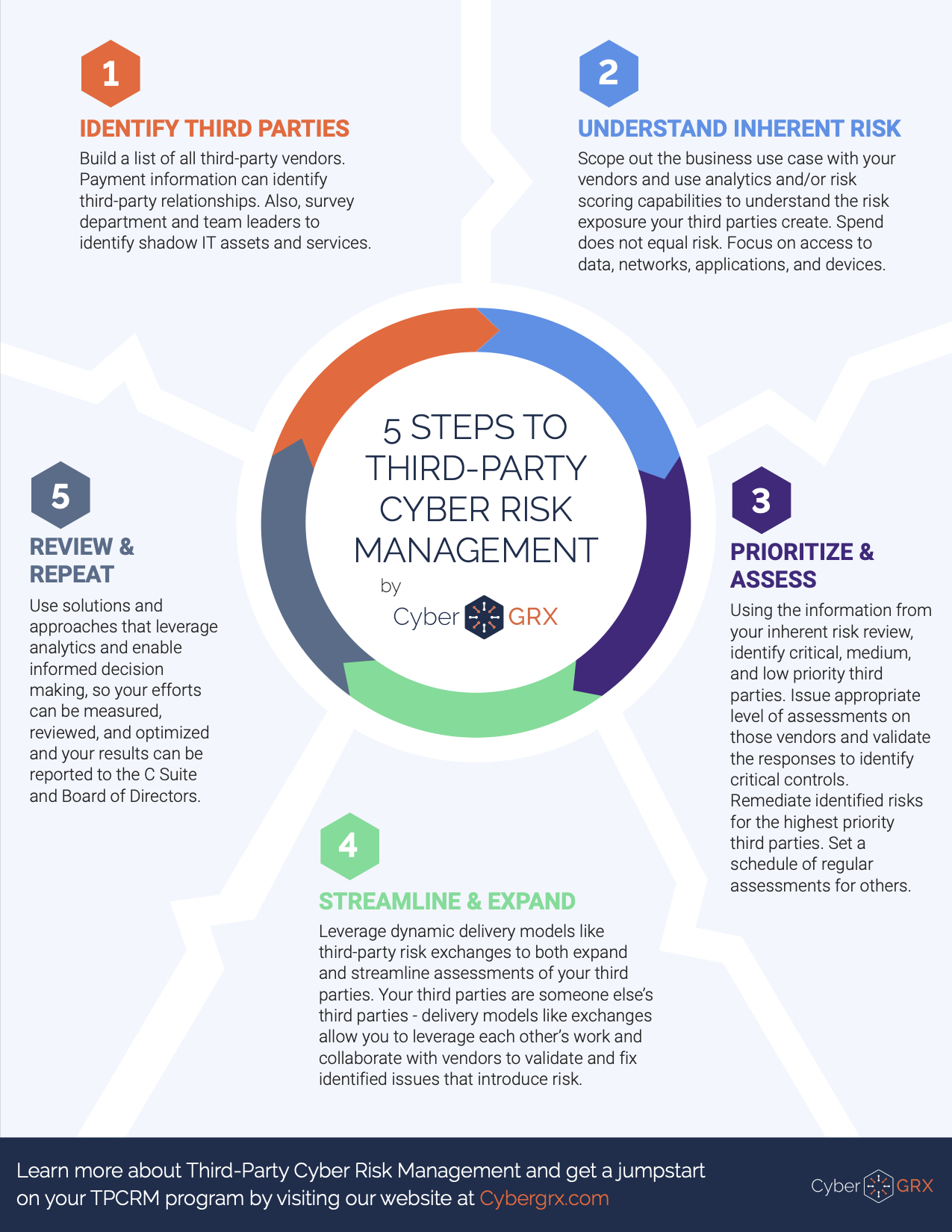
5 Steps to Third-Party Cyber Risk Management Infographic | CyberGRX

BroadBand Nation: Cybersecurity Career Pathway (INFOGRAPHIC)
![10 Cyber Security Tips for Small Business [Infographic]](https://www.signix.com/hs-fs/hub/40624/file-1738253956-jpg/images/ncsa_small_business_infographic.jpg?width=1800&height=4728&name=ncsa_small_business_infographic.jpg)
10 Cyber Security Tips for Small Business [Infographic]

Cyber Security Data Protection Abstract Concept Vector Illustration

CYBERCOM concludes CYBER FLAG 23 exercise > U.S. Cyber Command > News